
The Fabric
Corporate Cyber Conundrum
As Enterprises are looking at innovative ways to digitize and modernize, Corporate Leaders are demanding stronger evidence between the annual cyber spend and firms risk posture. Without clear understanding of business context and priorities, cybersecurity initiatives may result in unnecessary costs without potentially reducing risks where it matters.
Issues in Business' Cybersecurity Investments
Lack of Business Context
Limited Resources and Budget vs. Competing Priorities
Complex Operational Landscape
Ability to Communicate Business Value and Risks in Business Terms

.png)
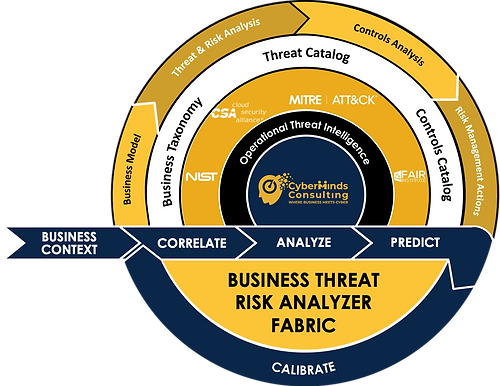
CyberMinds Solutions' Business Threat Risk Analyzer Fabric
CyberMinds Solutions' framework brings a unique, holistic, and structured approach by correlating business taxonomy, threats, risks, and controls into a measurable, traceable, and predictive outcome.
Built on the industry's best practices and standards, firms can perform end-to-end analysis and profiling of threats, risks, and across the entire business stack to focus on reducing the most significant risks.
For detailed information about The Fabric download the Whitepaper Here.

Advantages of the Business Threat Risk Analyzer

Cybersecurity measures are aligned with business needs.

Business assets are protected against the prominent risks it faces.

Enables shared understanding between Business, IT, and Cyber.

Verifiable and differentiated controls eliminate unnecessary costs.
Common Industry Use Cases

"The Cyber world tends to be operationally focused. Little effort is spent in creating a stronger operational-strategic alignment to deliver controls that can provide better and a sustained value to the business. The Fabric is our attempt to infuse business-architectural thinking & discipline into Cyber Initiatives. With clear linkages between controls implementation and business outcomes, CISO teams can effectively communicate the value of Cyber in a language Corporate leaders can understand. "